Internet Protocol stressers have become increasingly popular tools for malicious actors to carry out distributed denial-of-service attacks.
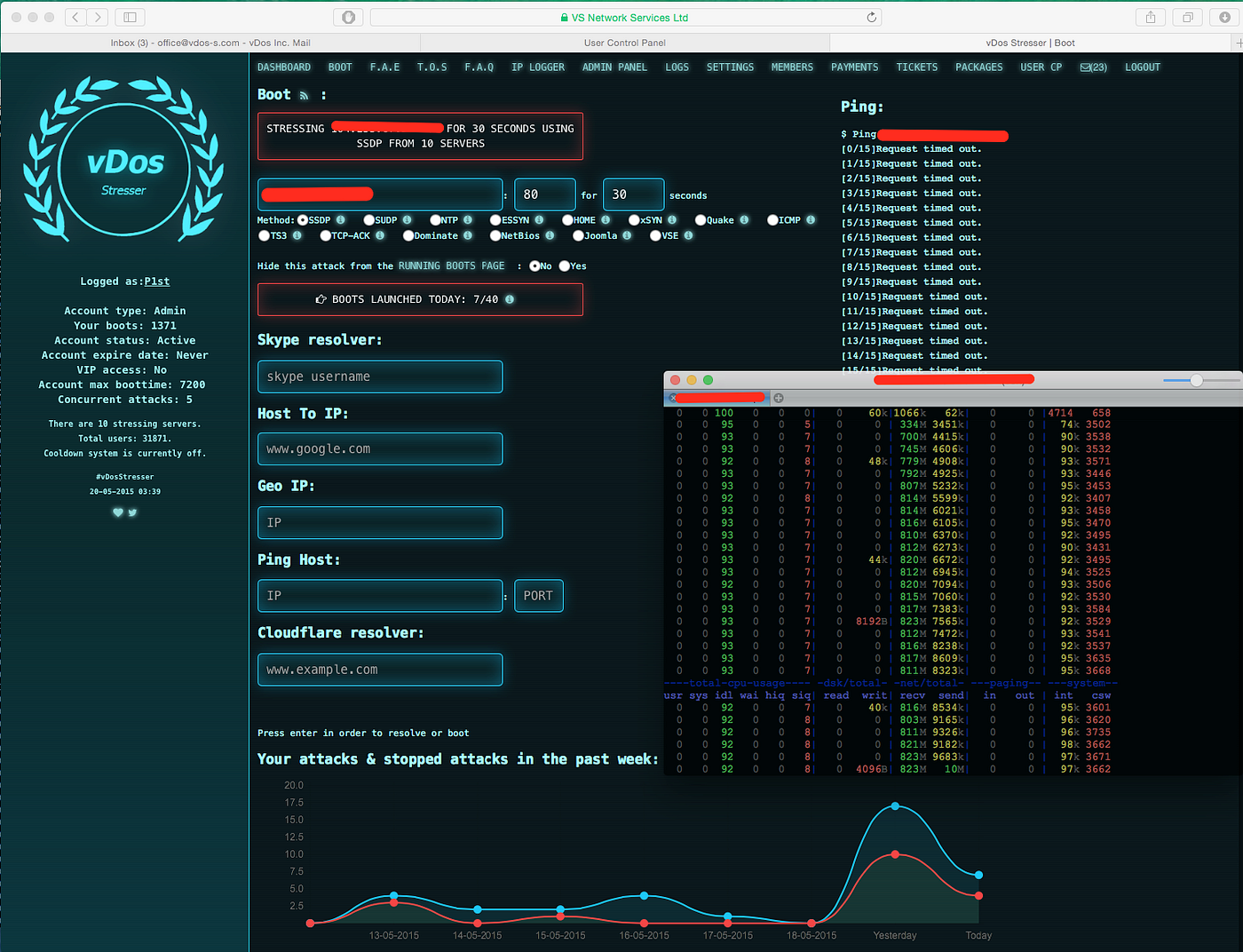
IP stressers are web-based services that provide users with the ability to overload and take down Internet-connected systems and networks through DDoS attacks. They work by enlisting a large network of compromised devices, known as a botnet, which then floods the target with more traffic than it handles, denying legitimate access.
Attackers essentially “rent” access to the botnet infrastructure of IP stressers to target any system of their choosing – typically sites and services they have a grudge against. Some IP stressers even provide “stress testing” services ostensibly to help site owners assess the resilience of their infrastructure. However, the overwhelming proportion are used maliciously.
How do IP stressers work?
- The IP stresser service itself, which customers access through a web-based interface.
- A large botnet of enslaved devices infected with malware like Trojans that allow remote control. Most botnets range from a few thousand devices to the millions.
- The command and control servers that control the botnet. Instructions from customers of IP stressers are relayed through these servers telling the botnet what target to attack.
what is the best stresser? From the web interface, users choose the target IP address or domain they wish to take down. They also tweak other attack parameters like duration or methods. The attack types offered depend on the specific stresser but include UDP floods, ICMP floods, ACK floods, and more. The customer then initiates a payment, which ranges from just a few dollars to hundreds of dollars per attack, depending on scale and duration. Once payment is verified, the botnet springs into action, flooding the target with malicious traffic that denies legitimate access.
What is the impact on targeted systems?
- Websites and web applications become extremely slow, unresponsive, or completely offline
- Company internet infrastructure like routers and firewalls are rendered inaccessible
- Cloud-based services and networks see dramatic latency spikes and downtime
- Online games lag, disconnect players, or their servers crash entirely
- Business operations are disrupted across organizations when vital systems and tools are unavailable
The outages directly translate into major revenue, productivity, and reputation loss for the victims. Attacks lasting multiple days also erode customer and employee confidence and engagement with online services. Even when attacks stop, the recovery process is lengthy. A barrage of malicious traffic often exposes weaknesses in the target’s DDoS mitigation capabilities. To properly protect themselves going forward, they need to implement updated network security protections. For home internet users part of botnets, the impacts include severe slowdowns in internet speeds during attacks. Their devices are also compromised as part of the botnet, posing privacy and security risks of sensitive data theft.
Motivations behind using IP stressers
- Revenge – Retaliating against people, companies, or groups they have personal grudges against
- Financial gain – Blackmailing victims for money to stop attacks
- Protest – Attacking sites and networks to make political or social statements
- Challenge/fun – Targeting high-profile platforms like Xbox Live and government sites for bragging rights
- Cover up other crimes – DDoS is used to cripple security systems while intruders break into networks
While their goals differ, they rely on the access to powerful botnets that services like IP stressers offer ordinary, less tech-savvy attackers. The increasing sophistication of booters combined with the surging number of vulnerable IoT devices like DVRs and webcams has led to the formidable DDoS capabilities available for rent today.