We all know how much we love our phones, don’t we? They can help us do everything from booking tickets, making plans, and keeping track of our finances—and they can help us take care of our loved ones too. We ...
The forecast for the construction sector looks bright with the growth anticipated in the commercial specialties. So the question is, can this be the right time to also grow your construction business? Although growth has its appeal, it requires serious ...
A company’s brand identity is defined by its logo. The logo distinguishes the company. This is the most potent attribute that can influence the image of your company. This post will demonstrate six reasons you should use a professional Gold ...
Technology has given wings to the games. Today you can find craze of various games among the individuals and can enjoy witnessing their excellence among them without even facing any further hazards. These games are creating historical moments in the ...
The world of credit finance is being altered by the emergence of bitcoin. Whole-system is possible due to blockchain technology, and since cryptocurrencies are fractional, anybody may use this regardless of their financial condition. What is the best way to ...
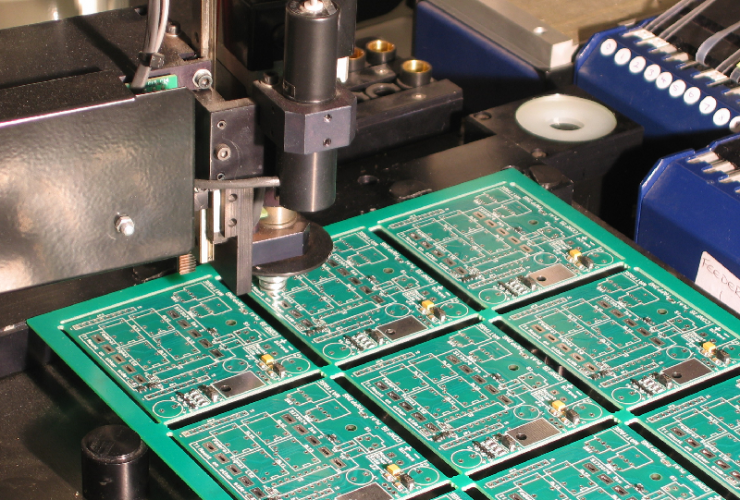
PCB or printed circuit boards are gaining momentum with time. They play a key role in production companies. As well as saving time, PCBs streamline manufacturing activities and cut down the overall cost. For these reasons, more and more businesses ...
Search Engine Optimization (SEO) is a must for any website to attract traffic. If you’ll be hiring a Brisbane SEO expert, you need to ensure that you get someone who will get you the results that you need. A good specialist ...
WordPress is a content management system that can be used to create a website. It has been around for over 15 years and is used by millions of websites as their CMS. A WordPress web design company designs, creates and ...
The CMMC (Cybersecurity Maturity Model Certification) is replacing the previous cybersecurity self-assessment process referred to as DFARS (Defense Federal Acquisition Regulations System), which made businesses contracted to figure with the Department of Defense (DoD) liable for their compliance. CMMC certification ...
Free AI Chabot. Yes, this is the new thing on the internet this year. People are looking for someone to talk to in these difficult covid-19 times. Isn’t it great that technology no matter how incomplete it is – finds ...